ID Card News
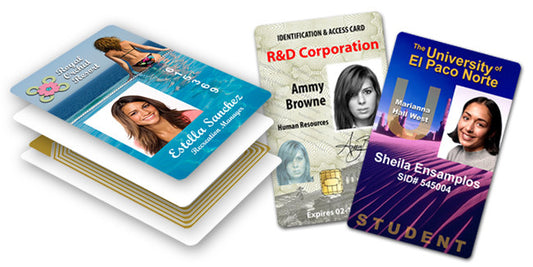
What are ReCarding Services?
Re-Carding can rapidly transform the security and reputation of a business, government office or school. Re-Carding eliminates internal headaches by outsourcing this challenging printing requirement.
What are ReCarding Services?
Re-Carding can rapidly transform the security and reputation of a business, government office or school. Re-Carding eliminates internal headaches by outsourcing this challenging printing requirement.

6 ways your passwords are stolen
If you lose your password to a criminal, your entire existence can be re-written, compromised, duplicated, and used against you.
6 ways your passwords are stolen
If you lose your password to a criminal, your entire existence can be re-written, compromised, duplicated, and used against you.

How do I protect my computer from hackers?
There are steps you can take to protect your information. Your ID card can be the key.
How do I protect my computer from hackers?
There are steps you can take to protect your information. Your ID card can be the key.

5 steps to a better Cyber Risk Management strategy
Information needs protecting! If one of your PCs is stolen, the cheapest part of the loss is the hardware. On average, it costs $509,000 USD in post-breach notification costs alone.
5 steps to a better Cyber Risk Management strategy
Information needs protecting! If one of your PCs is stolen, the cheapest part of the loss is the hardware. On average, it costs $509,000 USD in post-breach notification costs alone.
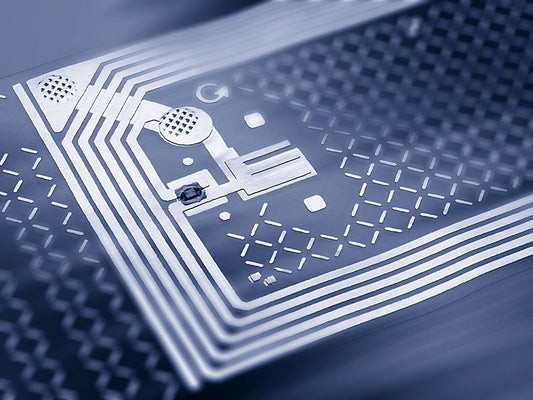
RFID Surveillance: Two Technologies Collide
For the first time, advanced tracking systems are combining the mature technologies of CCTV video surveillance and RFID tracking, resulting in a visual ability to trace tagged assets.
RFID Surveillance: Two Technologies Collide
For the first time, advanced tracking systems are combining the mature technologies of CCTV video surveillance and RFID tracking, resulting in a visual ability to trace tagged assets.

3 reasons why you need to lock your Windows™
Every single day, valuable business and personal information is stolen by criminals impersonating real people. Pathetically weak passwords are a serious threat.
3 reasons why you need to lock your Windows™
Every single day, valuable business and personal information is stolen by criminals impersonating real people. Pathetically weak passwords are a serious threat.
