RFID Surveillance
For the first time, advanced tracking systems are combining the mature technologies of CCTV video surveillance and RFID tracking, resulting in a visual ability to trace tagged assets.
1. RFID
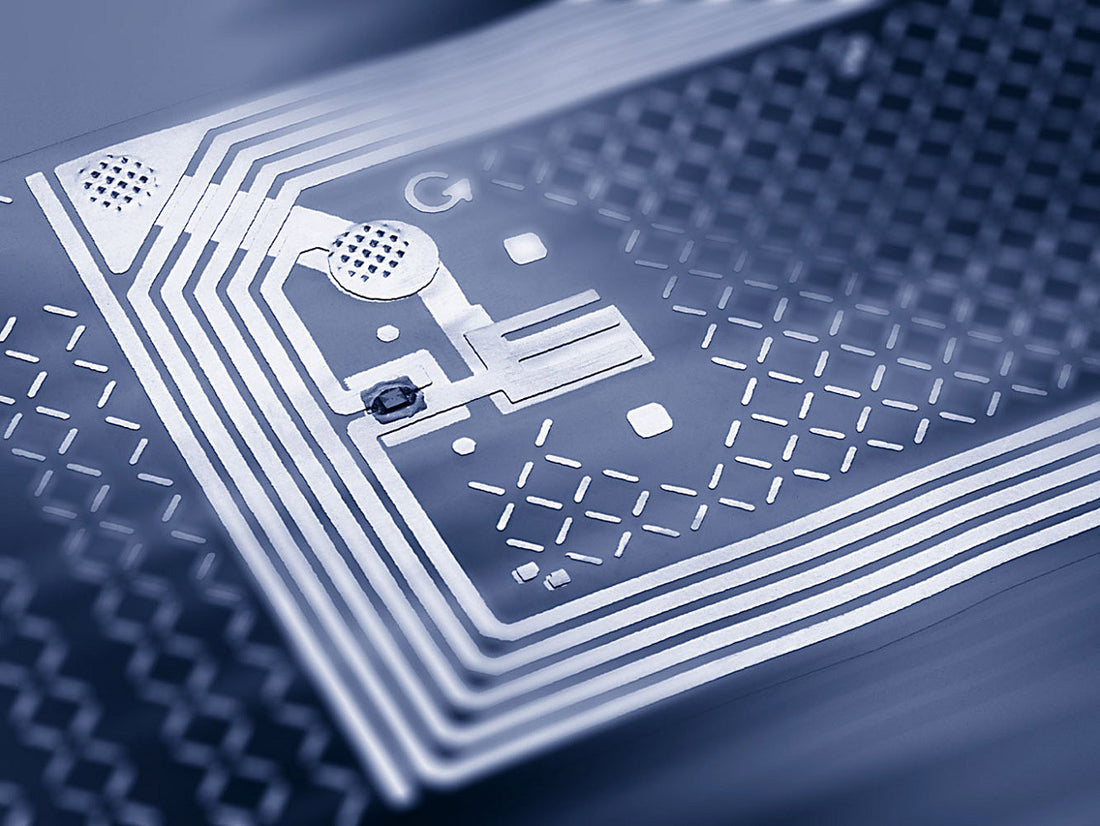
The use of RFID (Radio Frequency Identification) has been around for years, and refers to the wireless non-contact use of electromagnetic fields to transfer data. Like a lot of useful technology we take for granted today, RFID's first widespread use was military: the transponder used in Allied aircraft during World War II to identify an friend or foe. However, it wasn't until 1973 that a true RFID credential was patented - a passive transponder with memory, powered by an external interrogating signal. In essence, it was "reflected power", or power captured wirelessly by a device and used to transmit a signal of some kind.
There are three main frequencies used in contactless RF (radio frequency) communication:
- Low Frequency: 125 KHz
- High Frequency: 13.56 MHz
- Ultra High Frequency: 900 MHz and above.
In the world of ID cards and identification, 125 KHz frequency devices are often called "Proximity" cards, as they work within 3-4 inches of a reader.
Devices using 13.56 MHz are commonly referred to as "Contactless SmartCards" and UHF devices are often associated with the term "RFID".
| Why the need for a higher frequency?
Radio Frequency devices use radio signals, or "waves" to transmit the information. The wave has a peak and a trough, corresponding to a binary value, which is either a zero or a one. By condensing the wavelength so the peaks and troughs are closer together, a lot more information can be communicated in the same period of time. As the use of RFID for data transmission and collection became more widespread the relative insecurity of the low frequency devices became know, and the need for encryption rose. By using a higher frequency, enhanced encryption could be incorporated: a massive amount of data could be exchanged as part of the communication process. Today, may RFID applications use the HF and UHF frequencies not just because of security, but also because of the large amounts of data that can be exchanged. |
RFID can be used in a wide variety of applications:
- access control
- asset tracking
- tracking persons and animals
- data, toll or payment collection
- travel documents (Passports, Nexus cards etc.)
- airport baggage logistics
- inventory control
- airplane parts lifecycle management
2. CCTV
Video surveillance via CCTV (Closed Circuit Television) is rapidly becoming a significant factor in asset protection and loss prevention. Although it has been around since the 1950's, CCTV's recent growth has been explosive with the arrival of IP-based systems and non-proprietary storage devices. Video Surveillance is the cornerstone of many security systems, and has excellent forensic value in "after the fact" analysis.
Putting Things Together
Until very recently, RFID and CCTV existed as mutually exclusive technologies, useful in their own environments but never used in combination. That is all about to change. By marrying RFID and CCTV, the real power of visual tracking is realized.
| Picture this: a laptop in a server room is tagged with an RFID label. At the door of the server room there is an RFID reader, and a CCTV camera is installed outside the server room aimed at the server room door. When the laptop is moved from the server room, the RFID reader reads the tag on the laptop, combines the action with the live video stream coming from the door camera, and a record is created in the system database. When the security operator looks up the history of the laptop, they are able to click on the video link beside the tag number, and see the video of the laptop leaving the room, along with the face of the perpetrator carrying it! |
The applications for fighting crime and reducing losses are almost infinite. No two installations would be the same, as every asset and environment would be unique. Finally, a system exists which shows us exactly, in the most visual way possible (video), what the tagged asset is really up to.