The IDEXPERTS Difference
When IDEXPERTS opened our doors in 1996, we wanted to be different. There's more than one way to do business, and we recognized that there was a better way to sell ID products. We had experience in a range of industries, and we had the expertise that not many people in this industry did. Therefore, we decided that we wanted to be more than just another supplier.
We see business as more than just buying and selling. Which is why our goal has always been to create a relationship based on trust and expertise.
ID Card Supplies

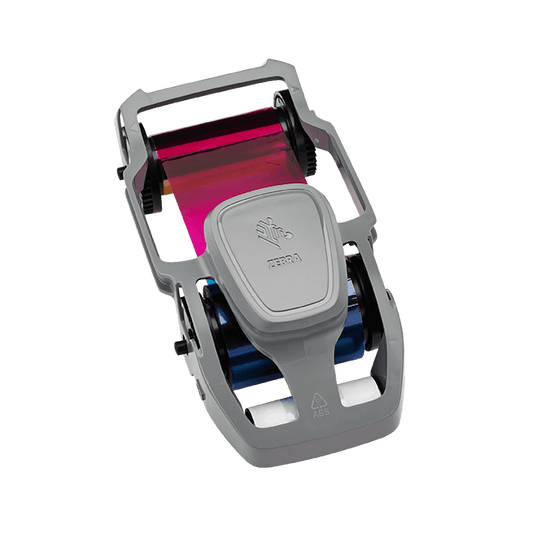
Card Printer Ribbons and Cartridges
Card Printer Ribbons for every make and model.
Thermatek™ CR80 30mil Blank Cards (100 pack)
Some of our services
-

Campus E-CARD
Find out what Campus E-CARD can do for youA suite of transaction management products and services applicable to any-sized school or post-secondary institution. Our wide range of services includes print management, laundry services, e-commerce, reservations, and more. Whatever your needs are, we can custom build a system to meet them, with room to scale up or down as needed.
-

We do more than "just" ID cards
Take a look through some of our past success storiesAlthough IDEXPERTS supplies organizations like yours with card printers and necessary supplies, that is not all that we do. We also work with a wide range of companies, government entities, post-secondary institutions, and a variety of other fields to build functional and secure systems that meet their needs.
-

Does it make more sense to outsource or to print your own photo ID cards?
Let's figure out your best optionSometimes buying a whole new printer system might make the most sense, but you end up spending more than you need. Or maybe you are already outsourcing your printing and you could be saving a fortune by printing your own cards.